Four-Step Strategy to Modernise IAM Systems and Mitigate Unauthorised Access Risks Explained in New Blueprint From Info-Tech Research Group
Comunicato Precedente

Comunicato Successivo

'With digital threats constantly evolving, IAM has become a critical focus for every CIO. The potential risks are significant: security breaches, data loss, regulatory non-compliance, insider threats, and reputational damage,' explains Ian Tyler-Clarke, executive counsellor at Info-Tech Research Group, UK. 'Despite its importance, many CIOs often categorise IAM as a 'hard & difficult' task. However, achieving success in IAM is not just about mitigating risks. It also enhances security posture, improves user experience, boosts operational efficiency, and strengthens risk management. IT leaders must embrace this challenge, though it is not without its complexities. By utilising Info-Tech's IAM Improvement Strategy Blueprint, CIOs can build a thorough and effective approach to IAM, transforming a complex challenge into a strategic advantage.'
The recently published resource from Info-Tech outlines common challenges faced by organisations in managing their IAM programs, including complexity, scalability, and cross-departmental collaboration. The firm notes that integrating multiple systems, applications, and directories can be especially difficult, particularly for organisations with large, complex IT environments. Resilience is also essential; as organisations evolve, IAM systems must scale to support more users, changing access needs, and new technologies like cloud services and mobile devices.
'A comprehensive identity and access management (IAM) program can enhance an organisation's security and operational efficiency. However, IAM programs are challenging to implement,' says Michel Hébert, principal research director at Info-Tech Research Group. 'Practitioners must collaborate with stakeholders to integrate systems, applications, and directories; address technical debt and outdated infrastructure; and balance robust security measures with a seamless user experience.'
Info-Tech's Key Steps for Building a Comprehensive IAM Strategy
In Develop a Comprehensive IAM Improvement Strategy, Info-Tech details a strategic four-step process that guides security leaders in implementing an effective IAM program. These steps ensure that organisations can enhance security, optimise processes, and align IAM initiatives with business goals:
Step 1: Assess Requirements – Align IAM goals with business objectives to enhance efficiency, ensure compliance, and reduce risks.
Step 2: Conduct Gap Analysis – Perform a comprehensive IAM assessment to identify strengths, gaps, and opportunities for improvement.
Step 3: Develop Policies & Workflows – Establish identity lifecycle workflows to lay the groundwork for program requirements and ensure that requirements are met.
Step 4: Build Program Roadmap – Prioritise IAM initiatives and communicate their benefits to stakeholders through a clear, actionable roadmap.
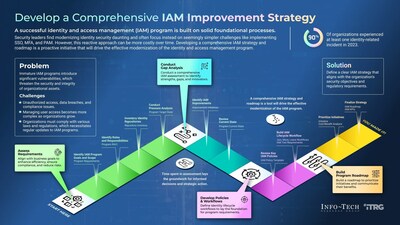
Info-Tech's comprehensive resource emphasises that security leaders should focus on proactive IAM modernisation rather than reactive solutions like single sign-on (SSO), multifactor authentication (MFA), and privileged access management (PAM). By taking a more comprehensive approach, organisations can create a resilient IAM system that aligns with their long-term security and business goals.
This new blueprint will provide security leaders with the strategic insights required to strengthen their IAM systems, ensure compliance, and enhance overall operational efficiency. In the resource, the firm highlights that clear communication and stakeholder engagement are critical for successful implementation, as IAM programs often require phased rollouts to deliver value over time.
For exclusive and timely commentary from Michel Hébert, an expert in security and privacy practices, and access to the complete Develop a Comprehensive IAM Improvement Strategy blueprint, please contact [email protected].
About Info-Tech Research Group
Info-Tech Research Group is one of the world's leading research and advisory firms, proudly serving over 30,000 IT and HR professionals. The company produces unbiased, highly relevant research and provides advisory services to help leaders make strategic, timely, and well-informed decisions. For nearly 30 years, Info-Tech has partnered closely with teams to provide them with everything they need, from actionable tools to analyst guidance, ensuring they deliver measurable results for their organisations.
To learn more about Info-Tech's divisions, visit McLean & Company for HR research and advisory services and SoftwareReviews for software buying insights.
Media professionals can register for unrestricted access to research across IT, HR, and software and hundreds of industry analysts through the firm's Media Insiders program. To gain access, contact [email protected].
For information about Info-Tech Research Group or to access the latest research, visit infotech.com and connect via LinkedIn and X.
![]() View original content:https://www.prnewswire.co.uk/news-releases/four-step-strategy-to-modernise-iam-systems-and-mitigate-unauthorised-access-risks-explained-in-new-blueprint-from-info-tech-research-group-302333239.html
View original content:https://www.prnewswire.co.uk/news-releases/four-step-strategy-to-modernise-iam-systems-and-mitigate-unauthorised-access-risks-explained-in-new-blueprint-from-info-tech-research-group-302333239.html

Ufficio Stampa
PR Newswire (Leggi tutti i comunicati)
209 - 215 Blackfriars Road
LONDON United Kingdom




